What data recovery tools to buy if you want to start a data recovery business?
Free video data recovery training on how to recover lost data from different hard drives?
Where to buy head and platter replacement tools at good prices?
Data recover case studies step by step guide
I want to attend professional data recovery training courses
Data recovery 001: What’s data recovery
Retrieving deleted/inaccessible data from electronic storage media (hard drives, removable media, optical devices, etc…). Typical causes of loss include: Electro-mechanical Failure, Natural Disaster, Computer Virus, Data Corruption, Computer Crime, Human Error, etc.
Data recovery 002: Uses of data recovery
-Average User: Recover important lost files; Keep your private information private
-Law enforcement: Locate illegal data; Restore deleted/overwritten information; Prosecute criminals based on discovered data
Data recovery 003: Software Recovery of data
* Generally only restore data not yet overwritten.
* Do not work on physically damaged drives
* Undelete Pro, EasyRecovery, Proliant, Novanet, etc.
* Prices range from Free-1000
* Example: dd on linux used on corrupt floppies
Data recovery 004: recovery methods
Hidden files
Recycle bin
Unerase wizards
Assorted commercial programs
Ferrofluid
Coat surface of disk
Check with optical microscope
Does not work for more recent hard drives
* When data is written – the head sets the polarity of most, but not all, of the magnetic domains
* The actual effect of overwriting a bit is closer to obtaining a 0.95 when a zero is overwritten by a one, and a 1.05 when a one is overwritten with a one.
-Normal equipment will read both these values as ones
-However, using specialized equipment, it is possible to work out what the previous “layers” contained
Steps include
* Reading the signal from the analog head electronic with a high-quality digital oscilloscope
* Downloading the sampled waveform to a PC
* Analyzing it in software to recover the previously recorded signal.
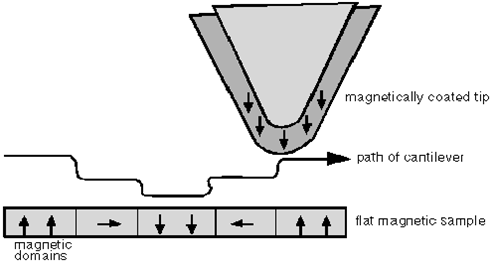
Scanning Probe Microscopy (SPM)
* Uses a sharp magnetic tip attached to a flexible cantilever placed close to the surface to be analyzed, where it interacts with the stray field emanating from the sample to produce a topographic view of the surface
* Reasonably capable SPM can be built for about US$1400, using a PC as a controller
* Thousands in use today
Magnetic force microscopy (MFM)
* Recent technique for imaging magnetization patterns with high resolution and minimal sample preparation.
* Derived from scanning probe microscopy (SPM)
* Uses a sharp magnetic tip attached to a flexible cantilever placed close to the surface to be analyzed where it interacts with the stray magnetic field
* An image of the field at the surface is formed by moving the tip across the surface and measuring the force (or force gradient) as a function of position. The strength of the interaction is measured by monitoring the position of the cantilever using an optical interferometer.
Using MFM:
* Techniques can detect data by looking at the minute sampling region to distinctly detect the remnant magnetization at the track edges.
* Detectable old data will still be present beside the new data on the track which is usually ignored
* In conjunction with software, MFM can be calibrated to see past various kinds of data loss/removal. Can also do automated data recovery.
* It turns out that each track contains an image of everything ever written to it, but that the contribution from each “layer” gets progressively smaller the further back it was made.
Data recovery 005: Secure Deletion-Government Standards
* Department of Justice:
DoD 5220.22-M – Type 1 degausser, followed by type 2 degausser, then three data overwrites (character, its complement, random)
* Problems with government standards
-Often old and predate newer techniques for both recording and recovering data.
-Predate higher recording densities of modern drives, the adoption of sophisticated channel coding techniques, and the use of MFM.
-Government standard may in fact be understated to fool opposing intelligence agencies.
Data recovery 006: Techniques Secure Deletion – Avoiding Recovery
* Degaussing
-Process in which the media is returned to its initial state
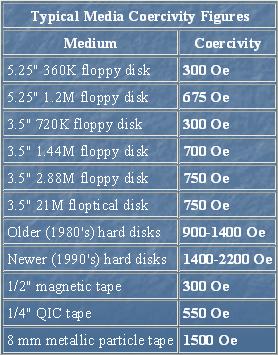
-Coercivity – Amount of magnetic field necessary to reduce the magnetic induction to zero. (measured in Oersteds)
-Effectively erasing a medium to the extent that data recovery is uneconomical requires a magnetic force ~5x the coercivity.
-US Government guidelines on media coercivity:
–Class 1: 350 Oe coercivity or less
–Class 2: 350-750 Oe coercivity.
–Class 3: over 750 Oe coercivity
-Degaussers are available for classes 1 and 2. None known for fully degaussing class 3 media.
* Technique 2: Multiple Overwrites
* Use an overwrite scheme
-Flip each magnetic domain on the disk back and forth as much as possible
-Overwrite in alternating patterns to expose it to an oscillating magnetic field.
-Overwrite with “junk” data several times
*Use the lowest frequency possible for overwrites
-Penetrates deeper into the recording medium
* Peter Guttman’s overwrite scheme:
-Meant to defeat all possible recovery techniques (MFM, etc)
-Specifies 35 different overwrites
-Not all overwrites are needed if targeting specific recovery method (i.e. MFM)
* Extremely Extreme Physical Destruction
-Chainsaws
-Sledge hammers
-Drop in a volcano
-Place on apex of a nuclear warhead
-Multiple rounds from a high caliber firearm
Data recovery Salon welcomes your comments and share with us your ideas, suggestions and experience. Data recovery salon is dedicated in sharing the most useful data recovery information with our users and only if you are good at data recovery or related knowledge, please kindly drop us an email and we will publish your article here. We need to make data recovery Salon to be the most professional and free data recovery E-book online.







Comments are closed
Sorry, but you cannot leave a comment for this post.